Arthur Miller and John O'Brien discuss privacy and surveillance
BROADCAST: 1970 | DURATION: 00:56:14
Synopsis
Arthur Miller, author of "Assault on Privacy: Computers, Data Banks, and Dossiers," and John O'Brien discuss issues relating to technological privacy and surveillance.
Transcript
Tap within the transcript to jump to that part of the audio.
Arthur Miller "Although we feel unknown, ignored As unrecorded blanks, Take heart! Our vital selves are stored In giant data banks, Our childhoods and maturities, Efficiently compiled, Our Stocks and insecurities, All permanently filed, Our tastes and our proclivities, In gross and in particular, Our incomes, our activities Both extra- and curricular. And such will be our happy state Until the day we die When we'll be snatched up by the great Computer in the Sky."
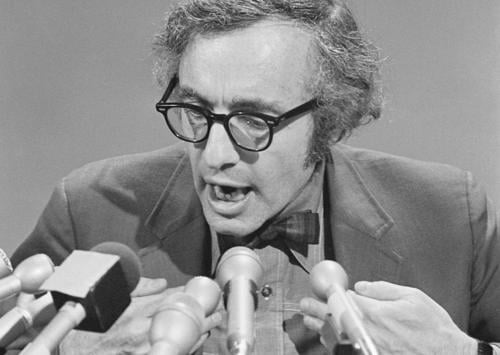
Studs Terkel That's a comic poem by Felicia Lamport that is read by Arthur Miller. It's the epigraph to his book, a frightening book and, yet, a very important book called "Assault on Privacy". Professor Miller teaches law at the University of Michigan, and the University of Michigan the publishers of the book. And it's a book that Nader, Ralph Nader, and Senator Ervin who figures very prominently in this matter with this committee dealing with surveillance, technology and what happens to us and sense of privacy. With Mr. Miller, Professor Miller, his guest is John O'Brien, whose name might be now familiar to many listeners. John O'Brien had the courage to blow the whistle concerning the Army surveillance of so many citizens both in office and out of office, and so both Mr. O'Brien and Mr. Miller will be sitting here talking about their experiences, and, well, this poem is funny, yet, it's not funny, is it?
Arthur Miller No, there's a very, very large and unfortunate grain of truth to it. I don't think most Americans are aware of the extent to which computerization is affecting our lives and altering past patterns and depriving us of a great deal of informational privacy.
Studs Terkel And you're pointing out that even though we live in a technological age, there's some advances made, yet what technology can do to us when it's used by people who are prying into the lives of other people. That humans do, humans do the programming.
Arthur Miller That's right. That's the great GIGO principle. Garbage in garbage out, that this is these vast and amazing electronic machines are really only as good as the data put into
Studs Terkel I think, John O'Brien, we can enter this, this is a free and easy conversation. Your own thoughts. For a time before you told us what was going on, you were working in Army Intelligence and in computers. I assume that data banks were used there, were they not? Or various technological devices?
John O'Brien Well, the data banks were used at the control centers. There were two. One was at Fort Holabird, Maryland, and the other one was with the counter-intelligence analysis branch. And, of course, at the level that I worked we provided the raw information that was eventually put into these data banks as refined information. And I don't think the Army could have really gone as far as they'd gone without the computers, without these large databanks.
Arthur Miller Indeed, it's a marvelous study of good and evil, as most modern technologies are. We couldn't run our Social Security system without computers and on the other hand, we couldn't have intelligence networks without computers.
Studs Terkel You used the phrase "dossier society." We seem to be living at this moment in the dossier society.
Arthur Miller That's right. On occasion I call it on the pathway to a dossier dictatorship, as well, unless we watch our steps.
Studs Terkel Yeah, you were quoting Jacques Ellul, a Frenchmen I know who has his worries about the machine.
Arthur Miller Yes.
Studs Terkel And what difference a totalitarian state if it's by the test tube, or the computer, or by hobnailed boot.
Arthur Miller That's right. Indeed, that's, to me, the theme of Orwell's "1984": A dictatorship by surveillance.
Studs Terkel I think what's become most prominent in the news is Army itself. Army --We'll talk about other aspects, FBI, CIA, and all related, I suppose, but Army Intelligence. And John O'Brien, you were involved with that for several years, weren't you?
John O'Brien Yes. Well, Army intelligence is not the horrible, unnecessary evil that it's been played up to be in many of the publications. It's a necessary arm of the military, and without the intelligence arm of the military, they cou-- The military would be unable to fulfill its function to society. But a very small aspect of that isn't un-- Or, presently is an unnecessary evil. It was when I worked for it, worked for Army intelligence. And that aspect is this tremendous overkill in the collection of information concerning the lawful activities and lawful expression on the part of individuals, Americans, who were engaging in unpopular issues, primarily the Vietnam War, the issue of the Vietnam War. And through this overkill, and on the part of many high-ranking military officials, the individual privacy of every American, not just those who happen to be liberal and walk on the street and carry the banners or the Vietcong flags and whatnot, but the privacy of every individual is threatened. What about the high school student who by virtue of his activity in the anti-war movement is investigated by Army intelligence? Well, how can a 17-year-old be affected by Army intelligence? Well, they won't be when they're 17, but this information that's placed in data banks and is made available to various federal, state, and local investigative agencies concerning this 17-year-old may have a dramatic effect upon him in later life. He will always be a subject of investigation no matter what he does, because of his activities while he was in high school.
Studs Terkel Were Army--high school students were surveyed or under surveillance by Army intelligence, weren't they?
Studs Terkel Yeah.
Arthur Miller Indeed, although one of the basic threats of file-building when it involves this type of overkill John is talking about, there's another aspect to it and that is the appearance, the appearance of repression. Even though you're not in a file, perhaps you start fearing that you might be in a file, and even though a file is never used against you, you begin to wonder, "Well, if there is a file, maybe they'll use it against me." Indeed, I think Justice Brennan of the Supreme Court put the problem most aptly when he, commenting on surveillance and wiretapping, said if it's carried to an extreme, that the result will be to encourage Americans to keep their mouths shut on all occasions.
Studs Terkel It won't be just silent majority quote unquote, but a silent unanimity.
Arthur Miller That's right. And of course, one of the things I believe that made this nation great and distinguishes us from so many other nations, is that we have a constitutional guarantee of speech and petition and assembly in the Senate.
Studs Terkel I'm thinking about your work and John's work. Both related in wholly different ways. Both of you have come to a similar conclusion, two opposite roads.
Arthur Miller Yes.
Studs Terkel Arthur Miller. This is--by the way, namesake of the playwright and both the fellow alumni of the same high school and university. You went to Harvard, I think,
Arthur Miller Yes, but I went to the same high school he did in Brooklyn.
Studs Terkel But in thinking the law and the dangers of technology and the dossiers on people, and John O'Brien, who had the courage to expose the very work in which he was involved, you know, in which Thompson, Nicholas, Senator Stevens, as well as a variety of other people, you know, who were not as well-known, were--in fact, some felt very offended that they weren't named on the list. I was! You know, I was very offended! I was
John O'Brien You haven't been active enough,
Studs Terkel Well, so, could we come--John, your own thoughts? I'm sure they're related to Professor Miller's thoughts. When did you have the feeling that something was wrong, that wasn't quite right, with the work that you were doing?
John O'Brien Well, initially here in this country, when I received my initial briefing, I was told our activities would concern primarily those who were engaging in activities to bring about a violent change socially and governmentally in this country. But when I saw the Stevenson file initiated by Army intelligence in September of 1969, I then began to wonder what right the Army had to engage in monitoring activities concerning a candidate for a federal office. And that's when I began to scrutinize my activities a little more closely and those of my fellow associates in the Army. That was the beginning, right there.
Studs Terkel Think, Professor Miller, to which purpose this can be used, do you--your book is full of all sorts of dazzling and terrifying information. The time-sharing network, this Army--Army John O'Brien worked for at the moment is unemployed, and in fact we can talk about that later on, the difficulty he has in finding a job at the moment, but the time-sharing aspect, I mean, this can be shared also by various agencies--
Studs Terkel Public and private.
Arthur Miller This is one of our problems of adjusting to the computer and protecting privacy in a computerized age. So many of our information gatherers and information handlers, you know, have a mentality that we're still in a quill and an inkstand type of environment where little sheets of paper are put away in manila folders which are then put in file drawers and that data exists at one time in one place. And that's the only threat. But we now have machines that can transmit information across the nation to another computer or to a terminal in a second or two seconds that provide on-demand copies at remote terminals. All you have to do is sit back and think of the way we monitor our astronauts when they're a quarter of a million miles away on the moon, and you begin to realize that McLuhan is right, that we live no longer in a book environment, in a paper environment, we live in an electronic environment, and information can move, it can exist in many places at the same time, and we have now a technology that enables us to prepare dossiers on every man, woman, and child in the United States, and store them in small packages, something we never could do before.
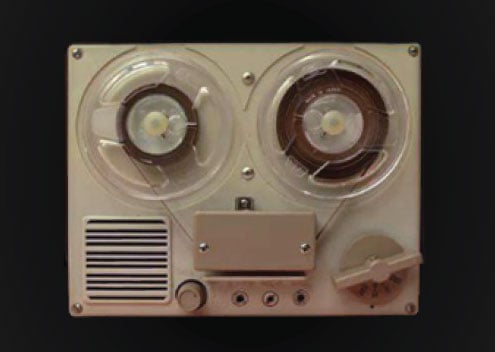
Studs Terkel It's a matter of a little tape, a little tape can have the entire life history of a man, can't
Arthur Miller That's right. Indeed, the new technology calls for the combination of computers and lasers and the implantation of information on magnetic tape by laser, and one man says that we now have the capability of taking just one long spool of tape, 4500 feet and putting a 12-page dossier on 200 million people on it. That's frightening.
John O'Brien I'd like to bring out an example of what the Professor has just stated. Every day, the Army intelligence command center at Fort Holabird, Maryland sends out via teletype to over 1000 other locations throughout the country other than Baltimore, a daily intelligence summary. All right, this is a teletype printout that goes across the wire. It takes about 10 minutes to prepare this. We're talking of maybe--well, we're talking of the--every event that had transpired the previous day that was recorded by Army intelligence that was thought to be of national interest. All right. Such as the Conspiracy Seven, the activities of the Conspiracy Seven trial were a good example. Any ghetto, militant ghetto activities, any anti-war activities were just among literally hundreds of categories. Well, the intelligence command had the ability, the electrical or the mechanical ability, to transmit this to 1000 different locations in the space of about 10 to 15 minutes from its central location, and from there it was transmitted into about 2000 other non-military offices. So here we have 3000 offices receiving information concerning the previous day's activities in a matter of 10 minutes. And it's all being sent across the wire, where 15 years ago, the information would have had to have been sent by mail. It would have been impractical. But today, it's a matter of just sitting down, typing the message out, and sending the tape across the wire.
Arthur Miller And it's not simply the speed, Studs, it's this miraculous technology in a sense gives us the ability to push more data through the system, and it's like Parkinson's Law.
Studs Terkel Parkinson's Law, therefore, you have to justify the machine.
Arthur Miller You justify the machine, you get the black box, and the automatic reaction is, "Well, now we have to fill it up." And I've seen some of this teletype material. And, my God, although some of it was extraordinarily competent intelligence work, some of it was the most unmitigated garbage I've
Studs Terkel So you have to get teletype material to fill all the apparatus that is there, and this could be naturally very personal, highly personal as, indeed, the FBI was trying on the late Martin Luther King, for purposes no doubt of keeping him quiet in his anti-war activities. But this, all these aspects are involved, too, aren't they? The highly personal things, too, did--John, was that a part of
John O'Brien As the Professor said, you have to fill the existing gaps, and due to technology, the military now has a spot report form with 14 categories, and all 14 categories there must be some information every time the report is sent forward. Something must be contained within, yet, I can remember on several instances where I collected information which would only fill seven or eight of these categories, but I had to fill in the remainder and send it forward. So the minute, unimportant intelligence information that was collected was passed forward and eventually found its way to the data bank.
Studs Terkel Professor Miller, there's something that John said earlier connected with this, too. He spoke of the thousands of offices, the 2000 non-military, in your book, "Assault on Privacy", you talk about this, too, the private companies.
Arthur Miller Yes.
Studs Terkel But is there a connection, too? Is there a cooperative aspect between the information collectors, private and governmental?
Arthur Miller Well, I think so. I have found that there is a great overlap between military intelligence people and law enforcement people and corporate security people, bank security people, insurance and credit investigators. Indeed, it's very common when a man leaves the military or police force to go into corporate security or bank security. And I think I have enough information on the basis of people who have visited with me, and material I've read, to form the judgment that, really, without malice or any intent at ill conduct there is just a professional exchange of information about people that goes on between governmental agencies and private companies. And again, that's an illustration of the fallacy of believing that information is physically located, because an insurance investigator may go out and do a field work-up on you, inquire about you of your neighbors, of your employer, your relatives. And lo and behold, that report will show up not only in the insurance data bank, but it will show up in the credit bureaus, it may show up at your employer's files, it may show up in a variety of federal agencies.
Studs Terkel Now, just as Arthur Miller is talking about this, John, in his book, "Assault on Privacy", University of Michigan Press, by the way, are the publishers of it, and has quite enthusiastic--I mean, terrifyingly enthusiastic comments by Ralph Nader, Senator Ervin, others, did you--in this thing, in Army surveillance, he talks about the visiting of neighbors and friends, sometimes it could be the matter of gossip that becomes part of the permanent history of the person, was that also part of the procedure?
John O'Brien Excuse me, yes, it was, to some extent. The good, the well-trained agent wouldn't pay any attention to the gossip, he wouldn't pay any attention to the rumors, and if he had hearsay information he so designated this information as being hearsay when he wrote the report. But when you take 1000 men and you throw them out into society performing the role of Army intelligence agents in this country, who are in constant contact with the public, and constantly seeking information from the public, you're going to have individuals who are not highly trained and highly competent, and as a result, this information, this hearsay, this gossip, the rumors, that does come to light during the course of many investigations is reported as being fact, and eventually ends up on the IBM printout as being fact.
Arthur Miller And multiply--
John O'Brien Multiply that by 15 agencies who receive the same information, multiply the 15 agencies by all their liaison contacts with other agencies, not necessarily federal, state, or local investigative agencies. And one report containing one rumor could eventually find its way right back to the individual's employer, find it back, find its way to the individual's insurance company.
Studs Terkel As he's talking, as John's talking, I'm thinking the--he mentioned 1000. This is 1000, just Army intelligence.
Arthur Miller Yes.
Studs Terkel Now, multiply this, I suppose, by all the other intelligence agencies private and public, what have we, how much of our population is involved now spying on everybody else?
Arthur Miller You know, there's a there's an interesting parallel to the military intelligence and that's the recent very embarrassing break-in to the media Pennsylvania FBI Center and the theft of 1000 documents, which, of course, I don't condone, but they did make interesting reading.
Arthur Miller And one of those documents, you talk about the chilling effect of surveillance on free speech, etc., one of the documents in the FBI file said, "Keep watching those activist organizations, let them know you're there, make them believe that there's an FBI agent in every garage. Let's make them paranoid." Well, you know, John says 1000 military people, there are thousands and thousands of insurance investigators and credit bureau investigators, and, again, there is this problem of poor training, poor judgment, the pressure of the system. There are companies which insist that insurance investigators file a certain number of reports every week and some of those people tell you that it's impossible to do a decent job on them all, so they fake it.
Studs Terkel Even, of course, I suppose one might add just ethically, even from the standpoint even with excellent work done, the very nature of the phenomenon itself, the phenomenon of surveillance and technology. You use a lot of euphemisms in your book, Arthur Miller, in his "Assault on Privacy", that are used: Optical scanners. And that means opening the mail?
Arthur Miller Now, well, that means reading the--at least the exterior of the mail with a specialized camera. Sure.
Studs Terkel Was that also part of a?
John O'Brien Well, you're getting--this is a very touchy area. First of all, I have never known the military to have engaged in the monitoring of mail. I am not that knowledgeable about the FBI doing it. However, I might point out that the military does have the capability of doing such because they do it in literally every other country in the world, and at the same time the military has an entree like no other federal agency has into the postal department, into the banks, into the credit unions. For some reason, the military can walk in and obtain information where, if an FBI agent was to walk into a bank and/or into the post office as an example, he would have to have a signed court order. The military doesn't need the court order. People are not afraid of dealing with representatives of the armed forces because they do not have any fear that this information is to be utilized for any other purpose other than the protection of the national defense.
John O'Brien They think, and in many cases this--in most of the cases this is true, but it only took six colonels to overthrow 12 or 14 generals in Greece, and my question is, we have 226 generals I believe in this country, and if we ever reach that point, I would like to know which ones would be in a position to effect the change.
Studs Terkel [Reading this sentence?], John is talking about seven days in May, are now coming in April. In a way. It's--
John O'Brien We're at 13 and counting
Arthur Miller That's right. The line I like when somebody says, "Do you fear '1984'?" I say, "Well, we're at '1984' minus 13 and counting," which is John Lear's line from "The Saturday Review".
Studs Terkel So where--this leaves us as we go further into your book and then to the experiences of John O'Brien, talking to Arthur Miller and John O'Brien, Professor Miller's book is "The Assault on Privacy", and John's own experience and observations and his courage in letting us all know about it, as a result his difficulty in getting a job. Here again, the aspect of fear. Obviously, John O'Brien is very expert in what he has done, as security in various industries. He's having a difficult time.
Arthur Miller I am very sorry to hear that, but as I'm sure John knows, it's not terribly surprising, is
John O'Brien No, I took this into consideration long before I wrote Senator Ervin that letter in December.
Studs Terkel We should point out that John wrote Senator Ervin and his committee--say that's a Senate committee on--
John O'Brien A subcommittee on constitutional rights.
Studs Terkel That first was exposing the nature of Army surveillance on American citizens, both in office and out of office, who may be dissenting or having unpopular views, that in some cases, became less and less unpopular certainly as concerns the war. But back to Arthur Miller and this book, what happened? You use the phrase "credibility gap," even in credit, now we come to the question of private lives. Yes.
Arthur Miller Yes.
Studs Terkel That is, all lives private, but lives not involving governmental work.
Arthur Miller It's a very simple proposition. Information is worth money in our society. Think of the tremendous credit network that exists in this country, and there is an industry known as the credit bureau industry, or the consumer reporting industry, I don't care which euphemism you use, that has as its stock in trade what it buys and what it sells is information about us, either for credit granting purposes, or for pre-employment investigation purposes, or for insurance purposes. And there is ample evidence on the record of the United States Congress over the past four years of tremendous abuse in terms of the quality of the information collected by these people and the frequently fraudulent methods used to extract this information from citizens. I have used the emotionally charged concept that some of these companies are informationally raping us when welcome newcomer comes to your door to welcome you to the neighborhood, it could well be that they are going to go back to some credit bureau office and file a report on you as to whether you need drapes, or what the condition of your furniture is like, and so on and so forth.
Studs Terkel And that could be something else, too, couldn't it, John? The welcome newcomer could be not only is this about involving credits and involving the way a person lives, but that also very often, too, is not the case. Remember the case of a switchboard operator at university passing on information about some dissenting philosophy professor to the FBI.
John O'Brien It was at Swarthmore College.
Studs Terkel Swarthmore, was it, yeah.
John O'Brien Well, not knowing the circumstances surrounding that, I would say that virtually any female contacted by the federal government, or I don't mean to discriminate against females, any individual in a position such as that contacted by the federal government under the pretext of seeking information concerning the activities of, perhaps, a controversial professor or seeking information concerning the activities of a violent prone organization, all you have to do is provide the information once, just once, and from that time on, you will provide or the individual will provide any information that federal agency so desires. This is a basic course taught in every intelligence school, that once you obtain information from a source the source is yours to do with as you please. And from my experiences, especially in Europe, this was always the case. There was never a rebellion on the part of the source. So, perhaps this woman provided information concerning phone calls from a professor's office. But if she'd been asked for information concerning, say, the president of the school, she would have eventually come up and given this information to the federal agency and most people like to cooperate with their government. So most people only don't think beyond, they don't question what the usage of the information will be. They want to cooperate. They feel it's their duty. And in many cases, it is.
Studs Terkel Isn't there also a fear here that if a person doesn't, is now coming back to the question of a dossier society, that Arthur Miller is telling about in his book and that you've been telling about in your way, in a dossier society, not a question of cooperating, but also a fear that I suppose I don't, in other words, maybe they will be looking at me a certain way, maybe somebody will be tapping my phone.
Arthur Miller Yes, there are a number of quasi-coercive ways that our government, not only the federal but the state and local governments as well, get information out of us. If you're on a welfare program, a Social Security benefit program, a Veterans Administration program, and a questionnaire comes to you, your instinct is that gee, either you are required by law to answer the questions, which is generally not true, although the government doesn't tell you that, or even if you appreciate the fact that most of these questionnaires are really voluntary, there is that lingering fear deep inside of you, "Will my check come next month if I don't answer these questions?" and very often that feeling is bolstered by the fact that there's a coercively worded follow-up letter or a nasty telephone call. I think John's point is really a very, very telling point, that we are very schizoid as a people.
Studs Terkel Yeah.
Arthur Miller We love our privacy, but let's face it, when the paper comes, we read Ann Landers and Joyce Brothers, we like to gossip. We like to cooperate with our government, and I must say that's a very healthy notion, we should cooperate with our government, but we also should be very, very sensitive as to the potential uses of information we give out, not only about ourselves, but about our fellow men.
Studs Terkel Of course, you're talking about the psychological effects on us, too, you're talking about people on welfare, and we know what happens to the privacy of people, you talk about this in your book, too, the effect of people on welfare when the social worker or whoever it is comes in.
Arthur Miller Yes.
Studs Terkel What must be told.
Arthur Miller Yes, you know, the knock at the front door is usually accompanied by a dive out the back door, a phenomenon we see not only when the welfare lady comes, but also unfortunately when the census man comes, and you know, this is one of the great ironies of modern information practices, we need the information to do a better job of allocating resources and servicing underprivileged populations, yet those are the very populations that are in a sense terrorized about some of these practices.
Studs Terkel Isn't that a new development here, I mean, that as people, a lot of people, a number of people have always been opposed to census, here a minority, but now it seems a great many people who are of minority groups worry because of the manner which they think census might be used because of what John O'Brien has been describing.
Arthur Miller Yes. In the old days, the bastion of anti-census feeling was in the sort of very conservative centers of the United States, the people who really believed in states' rights and limited government, and indeed that's, that resistance still exists. But the newer resistance is from, and this is the irony again, the very people who are likely to benefit from the census. They really are afraid, and I've talked to the people in the inner city, they're afraid that the census is a means for identifying them in times of crisis, to put them in concentration camps.
Studs Terkel Well, just as you're talking, wasn't there something in Arkansas, wasn't there a census, a certain kind of survey taken of 300,000 migrant kids?
Studs Terkel Migrant children, which raises a point, you
Arthur Miller The theory of that data bank and survey is to try and develop better record-keeping on migrant children so we can provide them with education fitting to their accomplishments, because a migrant child in Modesto, the next year he may be in Chittenango, New York and Chittenango won't have any knowledge of what he achieved in Modesto. This data bank is designed to make sure that the child gets progressive education, progressive healthcare. But when I looked into it, I discovered that nobody had ever thought about the potential harmful effects of this kind of dossier-type information, and people simply assume that this data might be made available to federal agencies and potential employers even though some of it was sensitive psychological testing and sensitive medical data. Again, this problem of insensitivity, not maliciousness, just unawareness.
Studs Terkel But it's because of what, using Army intelligence this is but one aspect as John O'Brien has made clear, 'cause of that the manner in which it may be used to stifle the idea of anybody disagreeing with whoever may be in charge, you see. But [might also be used?], obviously, in the question of migrant families, let's say Cesar Chavez fighting for the grape pickers or lettuce workers, see, or someone working with him. That could be used, could it not, it if fell into the hands of--
Arthur Miller You know, if one asks, "What is the most fundamental question here?" It is the one that John has raised.
Studs Terkel Yes.
Arthur Miller How do you accommodate this type of activity within a philosophical fabric of a democratic society?
John O'Brien I personally don't think that this type of activity in which I engaged and the type of activity the Professor has described here today was ever started with any malice, with any malintent. I think it evolved as it grew more complicated and as the individuals became less, well, shall we say, less sensitive to the complication in the technology that they were dealing with. And as a result, the individual no longer prevail. It was now a quota or there was a time period that had to be filled by those individuals, by the technocrats. And as a result we have some monsters that, let's face it, people, the people and the powers of the people to be, just don't want to do away with. They have this tremendous collection of information in front of them. They have this means through which they can intrude on anyone's lives, and they say to themselves, "But I'm not going to misuse the information," but inadvertently the information is misused. And very few people, humans, would be willing to give up that type of power.
Studs Terkel Of course, as Arthur Miller points out in the book, it is humans who do the programming. It is humans who handle the machines and if the value of a society may be cockeyed, you see what I mean? At a certain moment in its history, then, of course, it could be used to very anti-human anti-democratic purposes.
Arthur Miller Yes. One of the points here is that these systems tend to be controlled by people who have sort of tunnel vision. They have a mission, whether it be the military or the FBI or credit bureau or an insurance company and it's an in-house mission: Protect us against internal security. Give us law and order. Issue policies only to insurable people, cut down on our risks. And one of the problems is, as John suggests, that you have this accumulation of information power in the hands of people who are sort of looking at life through narrow parameters, and one of the great problems that I think Senator Ervin's subcommittee is going to face when it turns to the task, perhaps, of legislating, is how do we get wide-angle vision at the decision-making level when we create these systems in the first place? How do we make sure that all policies and all objectives are taken into account, not the simple narrow objective of a law enforcement agency or a military?
John O'Brien And then how do you see that such constructive legislation once it is written, first of all, could be passed on down to that to the individual working the computer or the individual in the street obtaining the information, that would be my first point. And then how could control be exercised and who would control this type of monitoring of the investigator, or monitoring of the spook, you might say?
Arthur Miller I wish I had easy answers to those two questions, John. We have it, we have an enormous problem of education in this country, an enormous catching up with technology. And on the second point, you're asking what, really, is an age-old problem. Who watches the watchers? And we've never solved that one. In a real sense, we're playing odds. We're playing mathematics. We know that no team plays 1000 ball, no batter hits 1000, we're just in a real sense trying to reduce the likelihood of abuse or misuse or an injury.
Studs Terkel In your book, Arthur Miller, "Assault on Privacy", and then John O'Brien's conversations and experiences and his comments, too, not just on this program, I mean publicly, more publicly, the question of psychological effect on us, on children, you call us children raised during a brain--you use the word "brain-watching" society, brain-washing also is involved there, too. What happens to us--even as I called John O'Brien on the phone. I was wondering, "Is the phone tapped?" You see, my own mind, see, or for that matter, calling you, since you wrote a book called "Assault on Privacy", is your phone tapped, or for that matter, is mine tapped? And so I'd like to use--I understand some Senator's aide did this--used profanity to open the conversation or some obscenity, I like to do that on the phone once in a while, as I was to clear the wire.
Studs Terkel But what happens to your own, to your own thoughts, you see?
John O'Brien Let me--if I could just get into this, first of all, it's very expensive, very difficult, to tap phones en masse. It's not too difficult to tap a single phone. All right. It's not so much whether or not your phone is tapped, or who's doing the tapping, but just the fear itself that it may possibly be tapped, and that fear itself has a greater damaging effect upon the individual than if he did know his phone was tapped. And this is the problem today. I know mine is not tapped because I, well, I'm familiar with tapping phones, but I would say 75 percent of the people who I've spoken to in the last two months always raise the question, "Is my phone tapped? How do I find out if it's tapped?" So I fig-- In my opinion these people were fearful for some reason that their phone wasn't tapped, in fact tapped.
Arthur Miller It's bizarre! I've met people in recent weeks who, as you say, they don't use profanity when they open the conversation. They start their conversation by talking to their tapper for a minute or so, or they talk in code.
Studs Terkel Yeah.
Studs Terkel I like to use profanity because it's good, it's sort of, it's therapeutic, it's also and maybe the person might hang up or might not, might feel offended because he's probably very, very moral.
John O'Brien But nine times out of ten, you're only talking to a tape recorder.
Studs Terkel I have to point. There's the horror of it now. Now we come to the horror. So it's a tape recorder I'm talking to.
John O'Brien Even your tapper's not human.
Studs Terkel Even the tapper isn't there.
John O'Brien No, it's the same notion of these bank video cameras or, you know, surveillance mirrors and cameras you see in stores. Most of them are nonfunctional. They're not operating. But once you see it, you don't know whether you're looking at one that is
Arthur Miller They have the deterrent effect. But unfortunately the government's activities has a reversal. It isn't a deterrent. Well, let me correct that. It's a deterrent to the individual who is exercising his basic freedoms. But it doesn't deter the individual from committing any criminal or political acts. He may think twice, about it but he's still going to do it even if he thinks his phone is tapped. I think organized crime has proven that. Organized crime has just as good a system of determining if their phones are bugged as the FBI does have in bugging them. and they still continue in their violent acts.
Studs Terkel I'm thinking on page 125 of Professor Miller's book, as John O'Brien was talking, a [quote?] through the microscope darkly, the handling of personal information by the federal government and you quote H. Taylor Buckner, and he says, "I see no reason to assume the government will be any more resistant to the pressures of the moment in the future than it has been in the past. Sending Japanese-American citizens to concentration camps would have immensely speeded" talking about World War II, "immensely speeded by having national identity and data file" which we have today, of course, and didn't have then. Is that it? Yeah. "And McCarthy could have destroyed" Joe, this is, "Could have destroyed many more careers if he'd had computer records of security investigations" and he didn't then, did he? He had some, but not as many.
John O'Brien And this is the point that bugs so many people. Again, going back to the discussion a few minutes ago about the census, the inner city people I spoke to in 1970 said, "The census is just a way of identifying us so they can herd us into concentration camps." Again, referring back to the Japanese, and when I'd say to them something like, "Come on, everybody knows where the center of the Black population is in various cities, they can't be using the census for that purpose." Their reaction was, "No, but the census will tell them how big to build the concentration camps, because they'll know how many of us there are, and who is to say we won't make another tragic mistake as we did in the '40s. Indeed, many of our mistakes in the last 30 years, McCarthyism, the Japanese concentration camps, were made in crisis environments.
Studs Terkel You know, we haven't talked about yet, and this involves both John O'Brien and Arthur Miller and John worked for the federal military intelligence, the connection, too, between federal, state, local matters. Here too, I suppose an interlocking, isn't there?
Arthur Miller Yes. Indeed, some of the interlocking goes on by authorization of statute, for example, to take a simple case, under our Internal Revenue Code there is a provision for exchanging tax data between the federal government and state and local governments. And already that is done in terms of 25 states by computer tape, it's just an exchange of tax data by tape. I'm sure John can speak to the intelligence exchange.
John O'Brien Well, there is an agreement between several federal intelligence agencies known as the Delimitations Agreement. And this provides for the extent of coverage and in what areas this coverage will be maintained by the different federal intelligence gathering agencies. At the same time, this agreement provides for the transmittal of intelligence information between one and all of the agencies. Now, it's very common throughout the United States for federal agencies to maintain close working relationships with associated state and local agencies. In the city of Chicago, the FBI transmits information on a daily basis to 11 agencies not associated with the federal government, that are not federal agencies. And also, they--well, I'm trying, but I can't remember the exact number, but also they transmit information to the Army, the Navy, the Air Force, the Secret Service, the Customs Bureau, and several other agencies within the Department of Justice. And at the same time, the local and state agencies look to the federal agencies for guidance, also look to them for this mass accumulation of information. So there's the connection between the federal and nonfederal investigative agencies here in this state.
Arthur Miller A good illustration of this, something I'm sure most of your listeners have seen on television, is the National Crime Information Center run by the FBI, and Efrem is always running an NCIC check on that, that's real. It's a massive computerized system operated by the FBI with thousands of remote access terminals out in state and local law enforcement agencies. At the moment it contains data on fugitives from justice and stolen property, which are legitimate because in both cases there's been a crime that's committed and it's very valuable data for a highway patrolman who doesn't want to get his head blown off approaching a suspicious car, he can run an NCIC check through his dispatcher. But what happens a year from now or two years from now in which more subjective data goes on or less accurate data? You know, the arrest records, for example, are not terribly accurate. In many cases they're misleading because they don't give enough information as to the circumstances of arrest or, what is even more common, there's no disposition indicated. There may--many people are arrested, but never prosecuted or convicted, or--and they're not criminals. What happens when NCIC or some of these law enforcement agencies start computerizing questionable data, inaccurate data, misleading data, and it starts circulating? We had in New York a frightening event four weeks ago, I guess it is, four consumer reporting agencies were convicted of bribing New York state policemen of illicitly procuring arrest records for these consumer reporting agencies. And that's a threat we've got to think about.
Studs Terkel You know, I'm thinking something else, too: this is the psychological aspects, the physical, the actual, the wildness, the promiscuity, in the passage of information, private, about a person's life. True or false, it really doesn't matter anymore, you know? But also the effect John was talking about, somebody who wants to cooperate, you know, with the government, and sometimes unquestionably, as to what the purpose may be, unquestioning. You quote Theodore Rozac, of the making of counterculture, Professor Miller does on page 54 of this book, "The Assault on Privacy". "For most of us, the jargon and mathematical aberrations of the experts are just so much mumbo jumbo. But we feel certain it is all mumbo jumbo that works, or at least seems to work. If those who know best tell us that progress consists in computerizing the making of political and military decisions, who are we to say it's not the best way to run our politics? If enough experts told us that Strontium 90 and smog were good for us, that was most of us would take their word for it. If we believe it's important to get there very, very fast despite the dangers, despite the discomforts, despite the expense, despite the smog, then the automobile is an impressive piece of magic, or you might say, SST." Come back to John's point, if THEY way up there say it's so, unquestioning we say it is so, perhaps the time has come for individuals to also question [quote?] matters of morality and ethics.
John O'Brien Let me bring up an example. In 1969 and 1970, the Army Intelligence Unit in Evanston conducted a series of investigations concerning the political activities of approximately 30 high school students attending the three Niles high schools. During the course of these investigations, the counselors at these various high schools were contacted and routine or what appeared to be routine investigations concerning the activities of the students were sought by these agents. Now the counselor was told that the individual or the individual's parents were being considered for a position of trust and responsibility with the federal government, and the counselor, these are current students I'm talking about--the counselor then provided information to the interviewer, who was an Army Intelligence agent. Among the questions asked were questions of homo-- concerning homosexuality, concerning the individual's moral character above and beyond the lewd activities one would associate with homosexualness, also political activity, alcoholic imbibing, and so on. My question is this. As a counselor, how could the federal government, especially the Army, have any legitimate interest in the political activities or the sex life of a 16 or 17-year-old girl in high school? Yet, the counselors never questioned this. They gave the information and with the exception of one administrator, and 30 interviews were conducted, with the exception of one administrator, everyone cooperated.
Studs Terkel So
John O'Brien Twenty-nine out of 30 cooperated. One refused.
Arthur Miller The flash of a badge or the showing of an I.D. card is one of the great door openers that man has ever created. We are very, very slovenly in terms of not thinking through what we do in the information field, and as that quote you read is designed to suggest, we just assume that everybody working for an organized agency of a government is exercising good judgment. Yet, we know mathematically that can't be true.
Studs Terkel Before you came, while waiting for you, Professor Miller, John O'Brien and I were talking about, he was talking about the apathy after his exposure. There were headlines, of course, and editorials and indignant comments by a variety of people aside from those who were quizzed, although our top city officials said, "I don't mind being followed," which would also indicate he doesn't mind others being followed, either, see. Aside from that, John, I, too, sensed an apathy, an acceptance, and so we come to the dangerous moment when people may accept their own debasement.
Arthur Miller Yes.
Studs Terkel Accept the diminution of their own rights.
Arthur Miller Everybody thinks it's the other guy in the file. You know, this marvelous combination of, "What have I got to hide? I'm a good Joe. I pay my taxes, I'm kind to my wife." The Spartan view of society, never thinking about the possibility of name confusion or misinformation dumped in his file accidentally or by a neighbor, never thinking about the millions of people in our society who may have an emotional chemistry a little gentler than he does. Never thinking about the philosophical basis of this nation and what it means to live in a free society, coupled with the marvelous astigmatism of a man who reads the paper 20 days in a row and he is told something on each of those 20 days and he simply doesn't put it all together for a jigsaw puzzle picture. We have had almost daily revelations about abuses of intelligence operations and abuses of technology now since John first spoke out. Yet, you talk to so many people and they just haven't put it all together, yet, in their own mind, they just don't see the emerging portrait. It's very sad.
Studs Terkel Where does this leave us? Suppose we have just some comments as all we're doing now is touching very, very lightly, by the way, on the experiences of John O'Brien and the book of Arthur Miller, University of Michigan, "The Assault on Privacy". It's an excellent one, by the way. Also deals with the question of technology in education. The good aspects of technology, technology and health, but the overall dangers of what it does to a man's own domain, his own private life. This book, suppose we have just comments, thoughts, on as it stands right now. John O'Brien, your own thoughts, on the way things stand, your own job, what you did, and yourself now.
John O'Brien Well, I don't think Professor Miller is going to like what I've got to say in this respect. Credit unions represent a problem to the individual but overall they cannot affect the national well-being, them by themselves. My thoughts along this line would be that the military, though, and you can't compare the two anymore, perhaps 10 years ago, the military can, through its intelligence-gathering operations, effect (sic) the national well-being of this country in a very short time. Many people have asked me, "What is the difference between the Army spying on the political activities of a civilian and the difference between the FBI?" The difference is very basic. The FBI is a small national police force, paramilitary in nature. They cannot go out and change the course of the political course of this country, directly they cannot. But the military is a very large, well-organized, regimented armed force, and throughout history, if we look back in history, not to be too much of an alarmist, the majority of your milit-- The majority of your revolutions from the established norm have been conducted by military men, or have been conducted by politicians with military backing. So I fear the military and their activities more than I would the credit union. The credit union will affect me when I go to get my job, but the credit union will not affect me politically, and will not affect my society politically. But the military can affect me in every way.
Arthur Miller Well, John, I don't think we really disagree. I think maybe we have different emphases which I think may be a function of our own experiences over the last year or two. I really do think there's a marked difference between the problem raised by military intelligence and the FBI. Sure, the FBI is not the threat that the military is. And on the other side of some sort of an imaginary line, the types of information intrusions and mistakes made by credit bureaus and insurance companies and employers, and there's no doubt in terms of the long-range health of our society, we need more protection against paramilitary and military groups than we do against private industry. I must say, when I when I started on this about five years ago, I started moving away from just being a very parochial technical law teacher and got involved in a variety of problems of technology and law. Nobody took this problem very seriously. I remember the debates in Congress on the national data center. I remember at that time I couldn't get federal agency officials to talk to me about safeguard systems and I must say, maybe it's the media screaming, maybe it's Congress screaming, maybe it's John O'Brien screaming, I don't know. But I now find a remarkable receptivity in a number of federal agencies toward the question of developing internal procedures for the safeguard of individual privacy. And of course, we're now seeing Senator Ervin's subcommittee energizing itself in the same direction. So to some degree, at this moment in time I am mildly optimistic that maybe we're plateauing now. I don't know, maybe I'm just too optimistic, but I do see the agencies and the Congress getting involved and trying to draw this fantastically complex and obscure line between legitimate data gathering and illegitimate data gathering, legitimate uses of the technology, illegitimate uses of the technology. And if we can just keep our eye on the ball and try to come to grips with this problem, maybe we'll solve it the way we're trying to solve the problem of the automobile and the airplane.
Studs Terkel We certainly can say that John O'Brien has performed a public service, a courageous one. Arthur Miller in his book offering us a terrifying at the same time important information. "The Assault on Privacy: Computers, Data Banks, and Dossiers", University of Michigan Press. You know, I think I ran into an FBI guy not too long ago and I offered him five copies of my book, autographed copies of "Hard Times", for one Xerox of my dossier. And he says he doesn't know. I don't know if he was an FBI man, a CIA man, or Army intelligence, I couldn't figure it out. I was going to make that trade, and he said no. Anyway, we--I think we know now. I think a great many Americans know now that brain-watching is one of the activities and brain-watching is certainly an Orwellian menace to a free society and to this must be alerted, and thanks to my two guests, too, for alerting us. Thank you very much.